What is IAM migration?
IAM migration is the controlled move of identity, authentication, and authorization capabilities from legacy systems to a modern IAM model. It matters because identity is now the primary security perimeter in digital transformation and zero trust architecture.
A well-designed migration improves resilience, user access consistency, and audit readiness while reducing credential risk.
Why is IAM migration important?
IAM migration is important because identity is now the primary security perimeter for cloud, hybrid, and multi-cloud environments. It enables stronger authentication, consistent access control, and better protection against credential abuse than many legacy systems can deliver. A well-planned migration also improves audit readiness and operational resilience while supporting digital transformation.
This strategic importance leads directly to execution design. After clarifying why IAM migration matters, teams must define a practical sequence that reduces risk and keeps user access stable.
What are the key steps in an IAM migration?
The key steps in an IAM migration are discovery_phase, strategic design, pilot validation, staged rollout, and post-cutover optimization. Discovery identifies identities, users and groups, applications, directories, APIs, and hidden dependencies; design then defines target controls, ownership, and rollback paths. Pilot and wave planning reduce disruption, while post-migration tuning confirms security posture and user experience outcomes.
With this sequence in place, organizations can choose the right architecture path for each workload. Strategy selection should reflect both near-term delivery pressure and long-term modernization goals.
5 phases of a successful migration
Select any phase to see key activities, risks to avoid, and success metrics.
Click any phase above to explore activities, risks, and metrics
Which IAM migration strategy is best for your system: rehosting, replatforming, or refactoring?
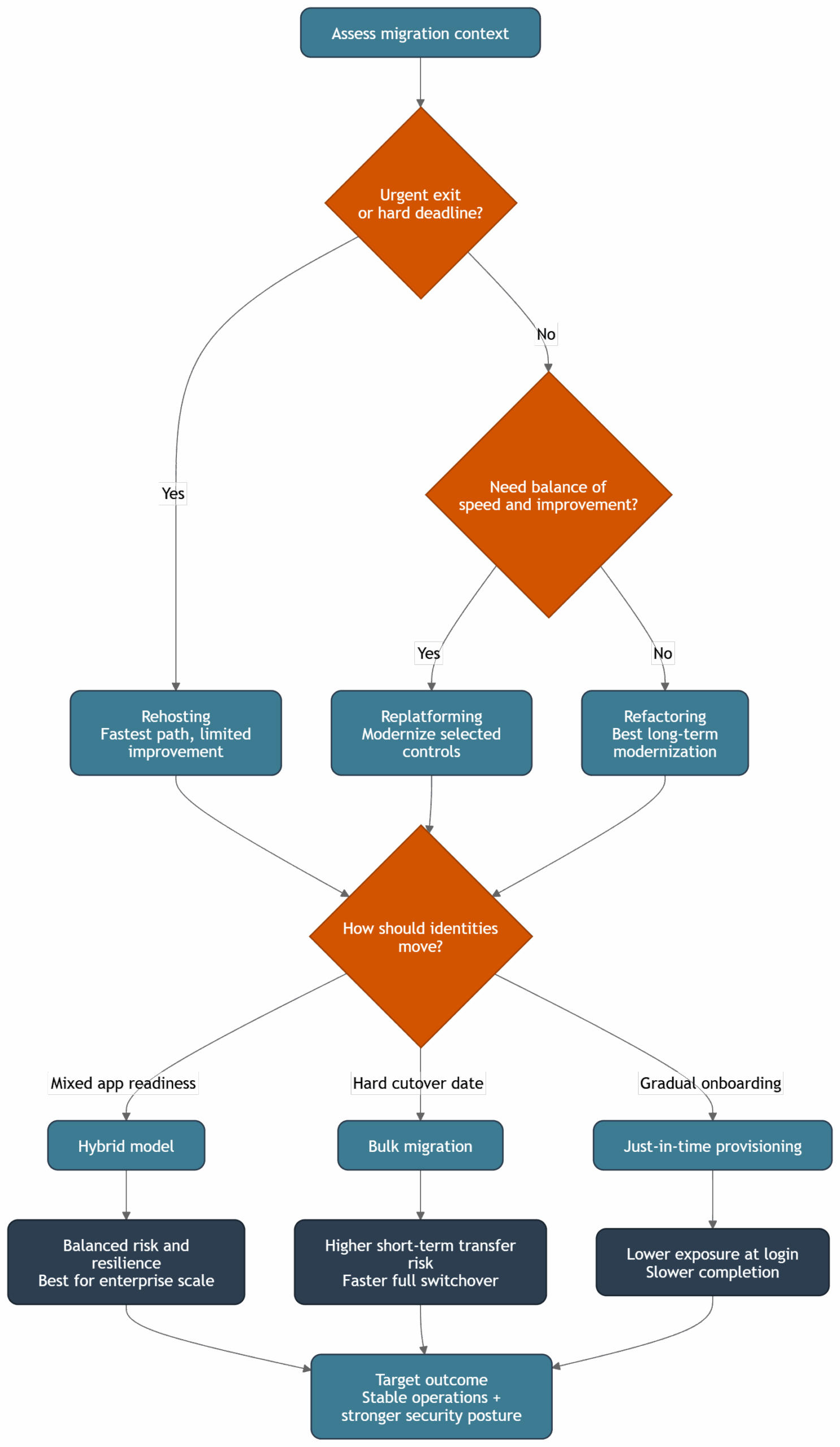
The best IAM migration strategy depends on business needs, risk tolerance, and legacy system complexity. Rehosting is faster for urgent exits, replatforming balances speed and improvement, and refactoring delivers long-term cloud modernization at higher initial effort. Most enterprises use a mixed strategy to minimize disruption while future-proofing security posture.
Once strategy is selected, the next design decision is what not to carry forward. This is where many programs either remove technical debt or accidentally preserve it.
Why should IAM migration avoid a pure lift-and-shift approach?
Pure lift-and-shift often carries technical debt, weak access control patterns, and legacy blind spots into the new system. IAM migration should be used to simplify policy design, centralize identity lifecycle controls, and improve authentication methods. This creates better visibility and control than copying old permission logic unchanged.
After eliminating lift-and-shift pitfalls, the migration must translate design choices into measurable security outcomes. The first benchmark is whether cloud IAM controls are stronger and more consistent than before.
How does IAM migration improve cloud security in hybrid environments specifically?
IAM migration improves cloud security by enforcing least privilege, stronger authentication, and policy-driven permission sets across hybrid environments. It also enables federated identity and short-lived credential models that reduce long-lived access keys exposure. Consistent controls across on-premises and cloud IAM reduce identity gaps that attackers often exploit.
To achieve those outcomes, execution discipline is critical. Programs that begin with structured inventory and wave design avoid the majority of preventable outages.
How should IAM migration start with discovery_phase and wave planning?
Start IAM migration with a discovery_phase that inventories identities, users and groups, applications, API dependencies, directories, and legacy systems. Then define wave planning for cutover windows, ownership, rollback paths, and user communication. This sequencing prevents zombie dependencies and lowers outage risk during cloud migration.
When discovery data is complete, access design becomes the next control point. RBAC mapping turns raw identity attributes into enforceable permission boundaries.
How do you map directory identity to cloud RBAC during IAM migration without privilege creep?
Map directory attributes to cloud roles using rbac_mapping, then validate least privilege outcomes for each type of access. In practice, teams map Active Directory groups to permission sets, IAM policy templates, and scoped roles in target platforms. The goal is to assign only required permissions, not replicate overly broad legacy access.
After role design, teams must decide how identities physically move into the new system. This choice drives both timeline and risk profile.
Which IAM migration model should you choose for your context: bulk migration or just-in-time provisioning?
Use bulk migration when deadlines are fixed and mass transfer is operationally acceptable; use just_in_time_provisioning when you want lower exposure and phased onboarding. Most enterprises choose a hybrid: JIT for active users and a controlled bulk pass for remaining accounts. This balances speed, security, and operational stability.
| IAM migration model | Best use case | Security profile | Operational impact |
|---|---|---|---|
| Bulk migration | Hard cutover date, large transfer window | Higher short-term transfer risk due to concentrated data movement | Higher initial workload, faster full switchover |
| Just-in-time provisioning | Gradual rollout, uncertain credential compatibility | Lower exposure because identities migrate at login | Distributed workload, slower full completion |
| Hybrid approach | Enterprise-scale, mixed app readiness | Strong balance of risk and resilience | Moderate complexity, best decision usefulness |
The migration model also affects platform integration choices. As organizations scale, they need a consistent identity source that still respects provider-specific controls.
How does IAM migration work across AWS Identity and Access Management, Microsoft Entra ID, and third-party identity provider ecosystems?
IAM migration in multi-cloud environments usually centralizes governance while integrating platform-native controls such as AWS IAM Identity Center and Microsoft Entra ID. Federated identity with an identity provider (for example Okta or Ping Identity) allows users to access AWS and Azure resources with consistent policy enforcement. This approach simplifies user management and reduces fragmented access management for AWS and other cloud platforms.
Cross-platform consistency is not enough on its own. Day-to-day operating models for human users and privileged workflows must also be hardened.
How should IAM migration handle federation, temporary credentials, and human users?
Require human users to use federation with an identity provider to access AWS and similar platforms instead of static local accounts. Use temporary credentials and tightly scoped permission sets for day-to-day operations, including devops workflows and emergency access runbooks. This model is central to zero trust and significantly reduces credential persistence risk.
With runtime access patterns established, governance can be formalized. Compliance controls should validate not only who can access systems, but also how that access is monitored and reviewed.
Which IAM migration controls are non-negotiable for compliance and audit trails?
Non-negotiable controls include MFA enforcement, centralized audit trails, least privilege reviews, privileged access pathways, and periodic access certification. Organizations should align these controls with SOC 2, GDPR, or HIPAA obligations depending on sector exposure. Policy quality matters as much as tooling because weak governance can invalidate strong platform features.
Governance only becomes credible when tracked through clear KPIs. Measurement closes the loop between migration intent and real production behavior.
Which metrics prove IAM migration success after go-live?
Track mfa_success_rate, orphaned_account_rate, login latency, failed authentication attempts, and access review completion. A practical target profile is MFA success above 98%, orphaned accounts below 1%, and visible reduction in repeated failed login patterns. These metrics show whether IAM migration improved both user experience and security outcomes.
These KPIs also expose hidden weaknesses quickly. The final planning safeguard is to anticipate common failure modes and design explicit prevention controls.
What are the most common IAM migration failure patterns, and how can you prevent them?
The most common failures are big-bang cutovers without rollback, incomplete inventory, messy identity data, and over-customized connectors. Prevent them with staged rollout, conservative scope per wave, strong test coverage for users or groups, and strict change governance. Communication discipline across business and technical teams is often the deciding factor between smooth migration and prolonged disruption.
Need expert support to implement IAM migration with Inteca?
Inteca supports end-to-end IAM migration programs: discovery, architecture, staged execution, and post-cutover optimization for cloud, hybrid, and multi-cloud environments. We help teams simplify IAM, improve access control quality, and operationalize federation, RBAC, and audit-ready governance. The result is a migration strategy that strengthens your security posture while keeping business operations stable.
See Inteca’s approach to IAM modernization projects
FAQ