CAS vs Keycloak: Which Identity Platform Should You Bet On?
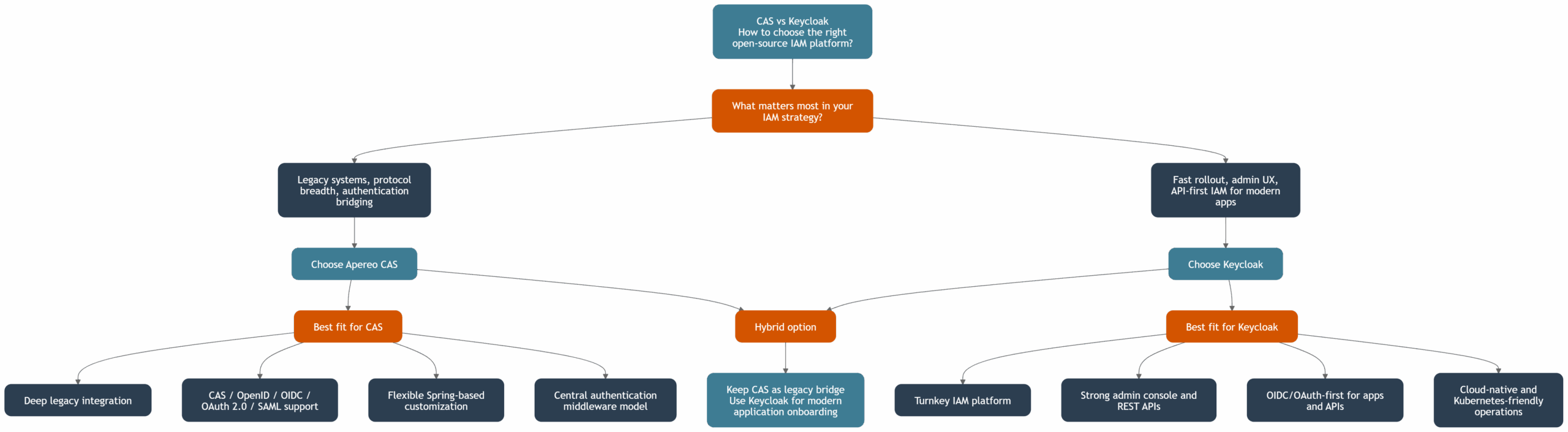
CAS vs Keycloak is a strategic choice between two mature open-source identity and access management platforms with different operating models. Both support single sign-on, authentication, and federation, but they differ in how teams configure, operate, and scale them. This decision matters most when you need to modernize an identity provider, reduce login friction, and improve access control for web, API, and legacy applications. That context leads directly to understanding what Apereo CAS is.
What is Apereo CAS in practice?
Apereo CAS (Central Authentication Service) is an open-source SSO and central authentication middleware focused on flexible integration with many authentication methods and legacy systems. A CAS server is typically built and customized with Spring-based configuration, so teams can delegate authentication to LDAP, Active Directory, databases, and external identity providers. CAS supports protocols like CAS, OpenID, OIDC, OAuth 2.0, and SAML, which makes it useful when protocol breadth is a hard requirement. That protocol-first architecture is easier to evaluate when contrasted with what Keycloak is.
What is Keycloak as an identity provider?
Keycloak is an open-source identity provider (IdP) and authorization server designed as a turnkey IAM platform with a strong admin console and API-first operations. Keycloak supports OIDC, OAuth 2.0, SAML, user federation, identity brokering, multi-factor authentication, and fine-grained authorization out of the box. Teams can authenticate users through local accounts, LDAP, or external IdPs, and validate JWT tokens in modern applications. This product-style approach sets up a practical CAS vs Keycloak comparison.
CAS vs Keycloak: what are the most important differences?
CAS vs Keycloak differs most in delivery model, protocol posture, and day-2 operations. CAS offers deeper middleware flexibility, while Keycloak offers faster onboarding through UI, admin APIs, and standardized workflows. The table below summarizes the key differences for architecture and operations.
| Area | Apereo CAS | Keycloak |
|---|---|---|
| Core model | Central authentication service middleware | Turnkey IAM platform |
| Primary strengths | Legacy integration, protocol bridge, delegate authentication | Modern OIDC/OAuth flows, strong admin console, developer onboarding |
| Protocol support | CAS, OpenID, OIDC, OAuth 2.0, SAML, WS-Fed (by module) | OIDC, OAuth 2.0, SAML (mature defaults) |
| Configuration style | Property/code-centric (YAML, overlays, Spring) | UI + REST APIs + realm model |
| Identity model | Strong external identity bridge | Internal user management + federation |
| Token model | Ticket-centric, with modern token options | JWT-centric for stateless verification |
| Multi-tenancy | Achievable via configuration patterns | Native realms |
| Kubernetes operations | Possible with custom packaging | Strong cloud-native path, operator ecosystem |
| Typical fit | Institutions with heterogeneous or legacy IAM | Enterprises standardizing IAM for apps and APIs |
These differences become critical when planning deployment and support ownership.
CAS vs Keycloak: how do deployment and operations compare?
CAS vs Keycloak operations differ in who does the heavy lifting: engineering teams in CAS, platform/admin teams in Keycloak. CAS usually requires deeper build and configure work, while Keycloak emphasizes a ready admin UI, predictable realm management, and easier API automation. In practice, both can run on-prem or in cloud, but Keycloak is often simpler for Kubernetes-first programs and faster first production rollout. The next question is whether modernization is needed at all.
CAS vs Keycloak: why move from legacy IAM systems?
Moving from legacy IAM systems is usually necessary to improve security, delivery speed, and interoperability. Legacy stacks often depend on brittle connectors, limited federation, weak API support, and inconsistent authentication policy enforcement across applications. Modernizing to CAS or Keycloak helps standardize identity management, improve user management, enable open-source SSO patterns, and reduce operational risk from outdated components.
| Legacy IAM pain point | Why it becomes risky | Modernization outcome with CAS or Keycloak |
|---|---|---|
| Fragmented login silos | Poor user experience and higher support cost | Unified single sign-on and centralized policy |
| Limited protocol support | Blocks new apps and partner federation | OIDC/OAuth/SAML support for modern and enterprise apps |
| Hardcoded app auth logic | Slow change and frequent defects | Reusable IdP patterns, adapters, and policy control |
| Weak MFA and policy depth | Higher account takeover risk | Multi-factor authentication and adaptive flows |
| Low automation and auditability | Compliance and incident response gaps | Better APIs, event logs, and governance readiness |
After migration drivers are clear, selection should be based on concrete use cases and team capabilities.
CAS vs Keycloak: which use cases fit best?
Choose Apereo CAS when you need a protocol broker for mixed environments, deep customization, and central authentication across many legacy integrations. Choose Keycloak when you need a fast path to standardized IAM, stronger default UX in the admin console, and broad support for developer teams using OIDC/OAuth and APIs. In large organizations, a hybrid pattern can also work: keep CAS as a legacy bridge and use Keycloak for modern application onboarding. This gives a practical decision framework before implementation.
Sources
-
Apereo CAS Documentation: https://apereo.github.io/cas/
-
Apereo Foundation: https://www.apereo.org/
-
Keycloak Documentation: https://www.keycloak.org/documentation
-
OpenID Connect Core: https://openid.net/specs/openid-connect-core-1_0.html
-
OAuth 2.0 Framework (RFC 6749): https://datatracker.ietf.org/doc/html/rfc6749
-
SAML V2.0 Technical Overview: https://docs.oasis-open.org/security/saml/Post2.0/sstc-saml-tech-overview-2.0.html
See Inteca’s approach to IAM modernization projects
FAQ