The first impression doesn’t happen when a contract is signed. It happens much earlier when a user, employee, or customer touches your system for the first time.
Good IAM onboarding process makes sure they land exactly where they should.
No delays. No confusion in the identity management process. No risk.
It’s not just about security.
It’s about user experience.
Whether you’re onboarding a new employee through an application or guiding a customer through registration – every click matters. Every second counts.
Done right, onboarding protects against breaches and directly impacts user activation.
IAM’s role in onboarding
User onboarding is the first real interaction between a person and your system. IAM decides what happens in that moment.
It gives users exactly the access they need. No more. No less. Right from the start.
Modern IAM handles:
- ensuring secure account creation,
- verifying identity in a way that matches both security policies and user comfort,
- managing consents aligned with regulations like GDPR,
- and automatically assigning the right roles and permissions.
If IAM is done well, users won’t even notice it.
They’ll just feel onboarding is smooth and safe.
This guide is for those responsible for ensuring that onboarding is not only secure but effective:
- CIOs and IT Directors building modern ecosystems
- Security leaders balancing GDPR with smooth UX
- Product owners and UX teams shaping onboarding people will actually enjoy
Whether you’re designing, fixing, or rebuilding onboarding — this guide is for you.

Inteca designs, integrates, and maintains secure onboarding flows
Inteca team behind secure onboarding
At Inteca, we specialize in solving exactly these kinds of onboarding challenges. We design, integrate, and maintain IAM solutions for cybersecurity – using Keycloak, open source software from Red Hat. Which powers the authentication and authorization processes behind many of the largest European platforms.
But we do more than just implement.
We help organizations shape onboarding itself – tailored to real users and real business logic.
Our knowledge doesn’t come from theory.
It comes from real projects, real platforms, and real users.
What is user onboarding in IAM?
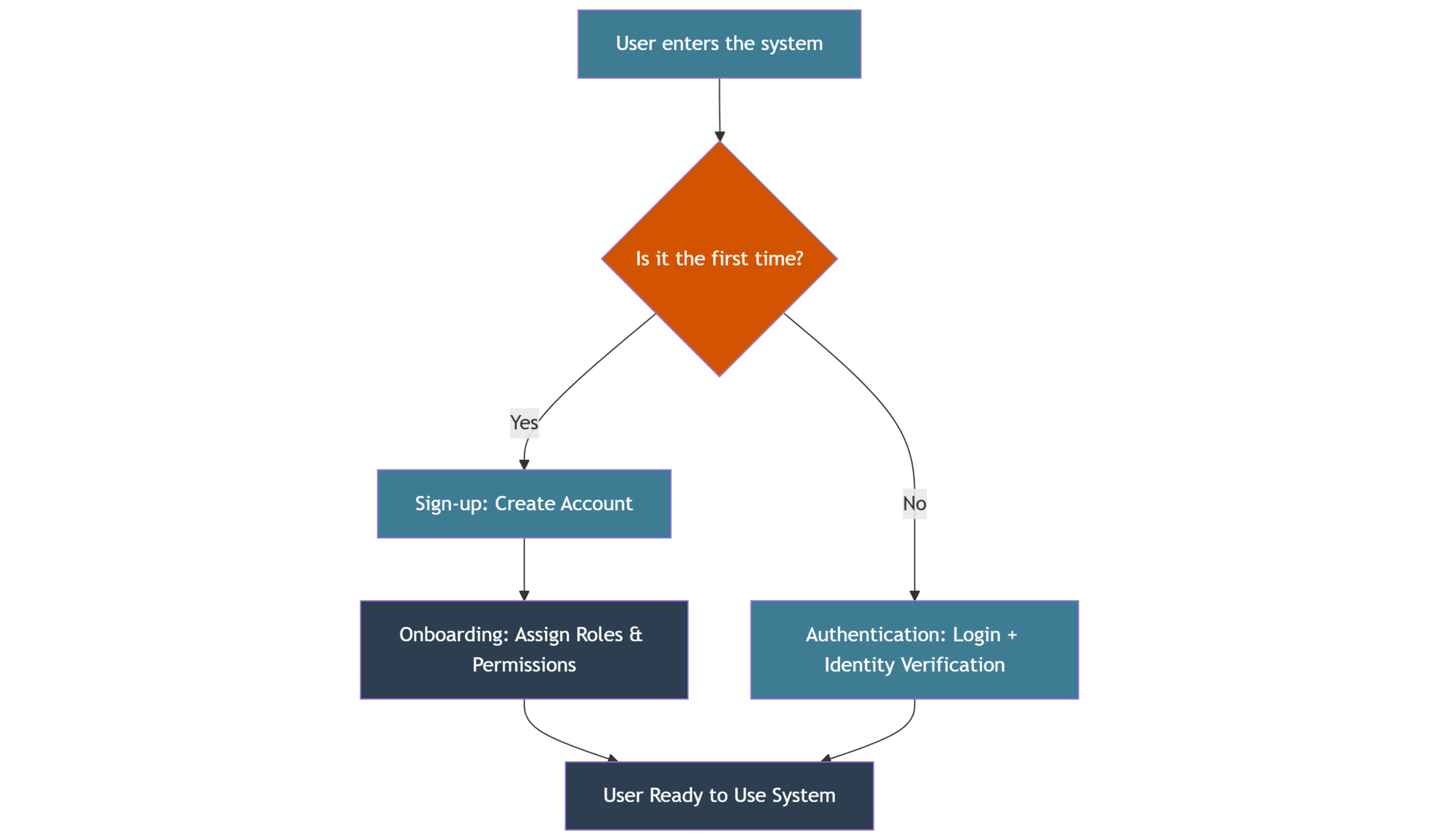
Onboarding vs sign-up
User onboarding is often confused with sign-up. But it’s much more.
In IAM, onboarding is the structured process of giving users — employees, partners, or customers — secure access to your systems. It’s not just registration. It’s about preparing them to work safely and smoothly from day one.
Sign-up? That’s the easy part.
It collects basic data and verifies identity — email, phone, maybe ID.
Onboarding goes further.
It sets access rights.
It assigns roles.
It guides users to the right services.
In short:
-
Sign-up = Create the account
-
Onboarding = Make sure the user is ready and secure to use your system effectively
Onboarding vs authentication
It is also important not to confuse onboarding with authentication.
Authentication is the step that happens every time a user returns to your system to log in and verify their identity. Onboarding happens once (or during migrations) when the user is being introduced, verified, and granted their first permissions. A clear onboarding process directly affects later stages of the IAM lifecycle, including authentication and ongoing access management.
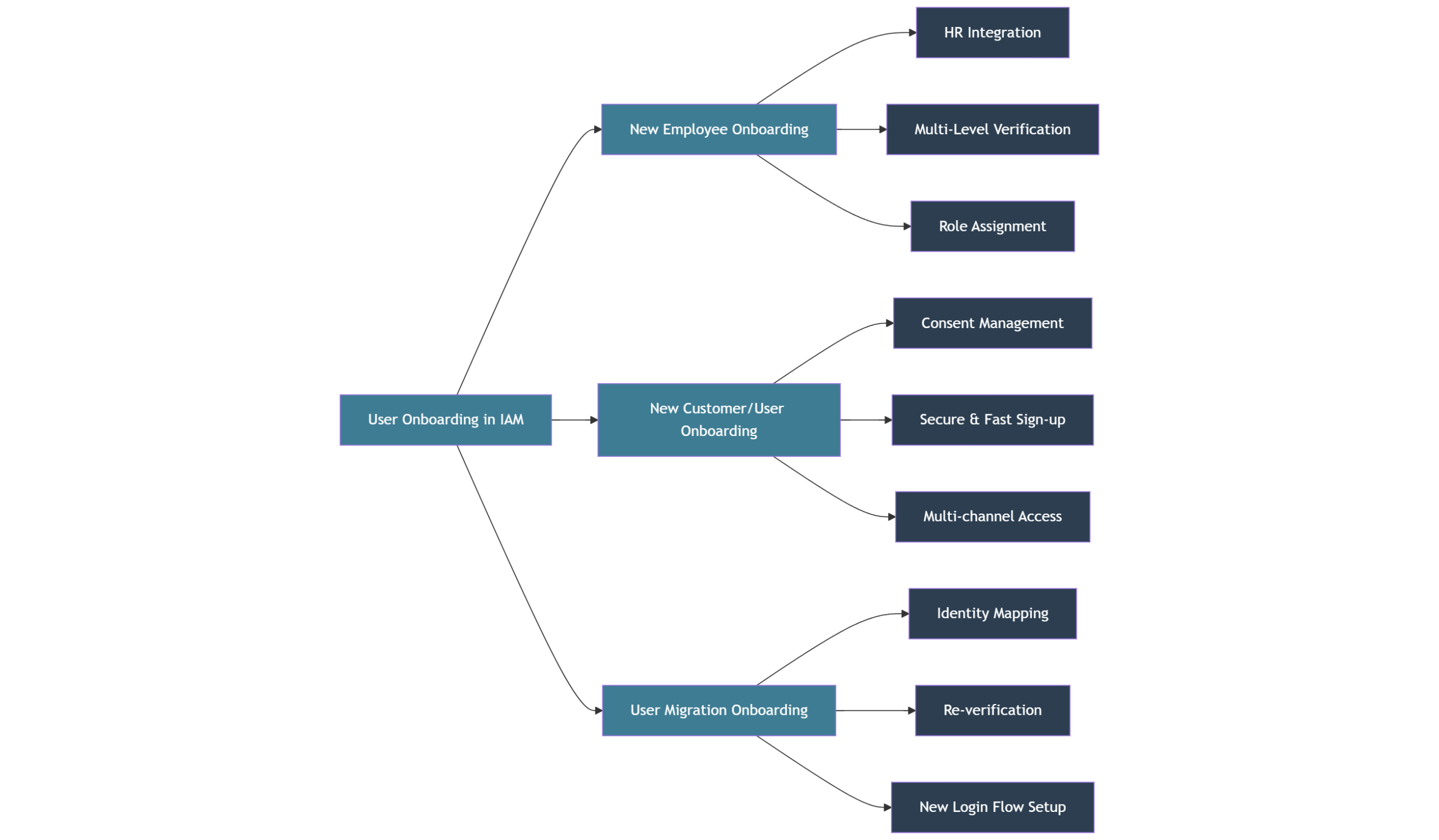
Types of onboarding in IAM
Organizations usually face three main onboarding scenarios, each with its own set of challenges and technical requirements:
-
New employee onboarding – integrating employees into internal systems such as HR portals, document management, business apps, or communication platforms. This scenario often involves multi-level verification, role assignment based on HR data, and access to sensitive internal resources.
-
New customer or user onboarding – for customer-facing services like banks, e-commerce platforms, public services. For mentioned onboarding needs to be fast, secure, and aligned with user expectations. This often involves consent management (GDPR, RODO) and the ability to provide various sign-up methods like passwordless login, SMS codes, or social login.
-
User migration onboarding – when your internal systems are replaced or expanded, organizations must migrate existing users to new environments. This can be highly complex requiring identity mapping, re-verification of existing users, or even onboarding them into entirely new login flows without disrupting their user experience.
Done right, onboarding serves as a bridge between security and user satisfaction, making sure that neither is sacrificed. For large organizations, it is rarely a simple task often it involves coordinating IT, security, UX, legal, and product teams.
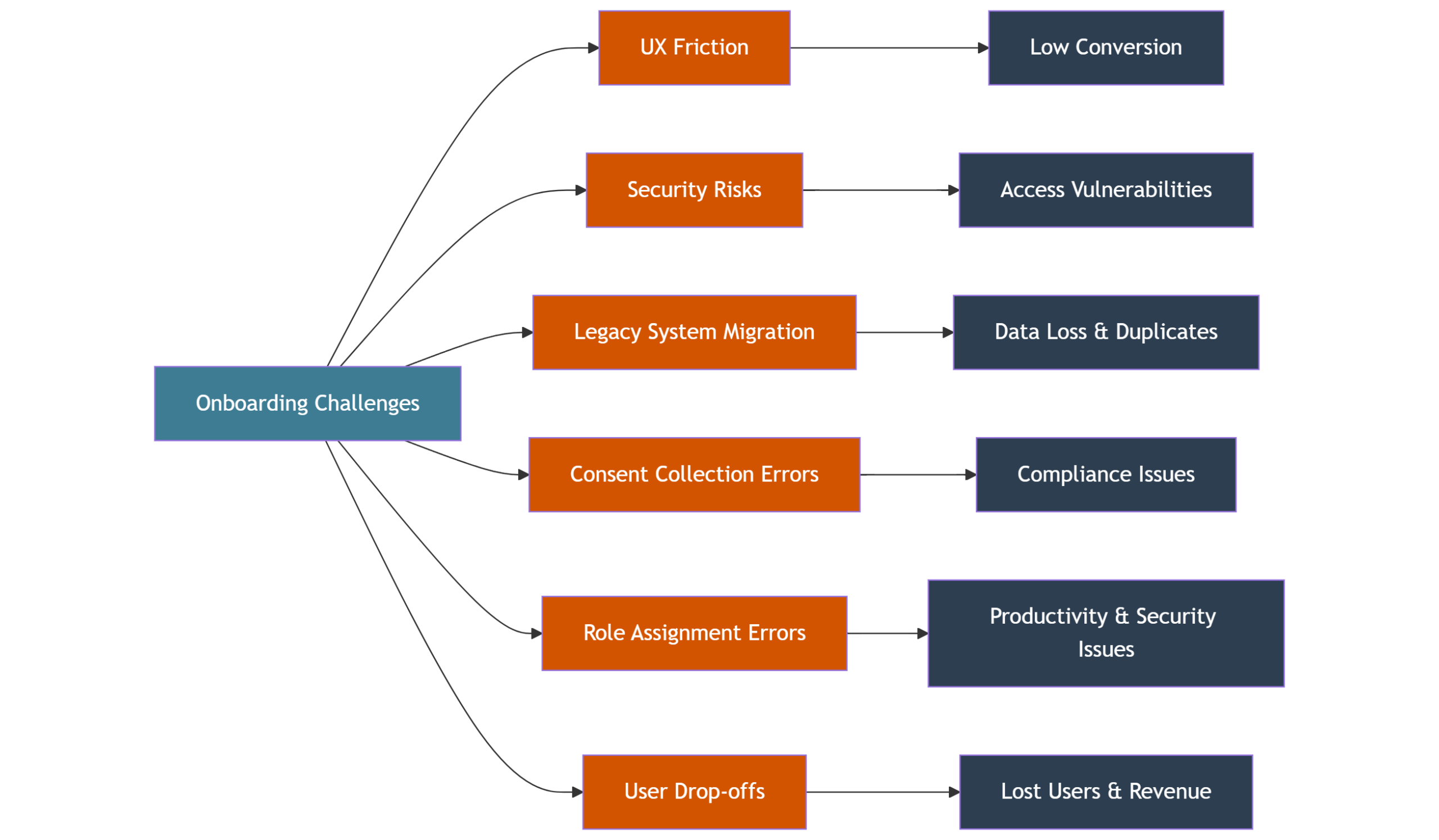
The Challenges of IAM Onboarding
IAM onboarding often looks simple on paper. In reality, it’s a place where things go wrong — both for users and for security teams. We’ve seen these problems over and over again.
UX friction, where good intentions fail
A long, chaotic onboarding kills conversion. 60% of users drop out when sign-up forms are too complex.
IAM onboarding often adds more friction — MFA setup, data consents, verification steps. These are needed, but without proper design, they feel like obstacles, not protection.
What’s the challenge?
Make it secure.
Make it simple.
Make it adaptable to the user.
Legacy system migration, complexity nobody wants, but everybody has
Most organizations don’t build from scratch. They migrate. That’s where trouble starts.
What happens?
-
Duplicated accounts.
-
Missing data.
-
Outdated authentication flows.
-
Users stuck between old and new systems.
DBIR1 confirms it misconfigured IAM migrations are among the top causes of access control incidents. We’ve seen clients juggling two onboarding systems during transitions. It creates confusion for users and headaches for IT.
Consent management, always urgent, often ignored
GDPR, RODO, CCPA – compliance isn’t optional. Yet, onboarding flows often treat consent as a checkbox, not a real process.
What’s the result?
-
Missing consents.
-
Users unclear about what they agreed to.
-
Legal risk waiting to happen.
IBM shows the cost clearly — $5.05 million per non-compliance incident 2. Consent isn’t paperwork. It’s part of onboarding security.
Role assignment, too much or too little access
This one is classic. Users get:
-
Too many permissions → security risk.
-
Too few → blocked work, more support tickets.
Manual fixes cause even more problems. According to LayerX, 25% of access violations are caused by role mistakes — often happening right at onboarding. 3
Roles are part of onboarding. Not something to “fix later”.
Drop-offs, the invisible leak
The most common onboarding problem? People silently leaving. No feedback. No complaints. Just gone.
-
37% drop-off if onboarding takes over 5 minutes.
-
20% never come back after failing the first attempt.
For customers that means lost revenue.
For employees, delayed productivity.
For security, more ad-hoc exceptions and risk.
And the hard truth?
These problems rarely show up one by one. They stack. Friction + poor migration + bad role logic = onboarding nobody is happy with.
| Challenge | Description |
|---|---|
| UX friction | Lengthy and complicated sign-up forms can discourage users from completing their onboarding journey. |
| Security risks | The first interactions can introduce security vulnerabilities if not managed properly. |
| Legacy system integration | Moving users from old systems can bring about complications and errors. |
| Consent collection mistakes | Missing the mark on user consent can lead to compliance headaches. |
| Role assignment errors | Incorrectly assigning roles can cause unauthorized access or limit functionalities. |
| User drop-offs | High dropout rates during onboarding might indicate a poor user experience. |
Turn your onboarding mockups into a working system
Best Practices for secure and effective sign-up
Good onboarding isn’t just about ticking boxes; it’s about enabling a smooth identity management experience. It’s about finding the balance — security without friction, control without chaos.
Here are the key ingredients every modern IAM onboarding flow needs.
Flexible sign-up flows
Not every user is the same. Not every onboarding should be either.
Give users options:
- Social login when it makes sense.
- Email and password when they prefer the old-school way.
- Passwordless when you want to be one step ahead.
Flexibility means less friction, more completed onboardings.
Modern IAM must adapt, the worst is to force every user into the same flow.
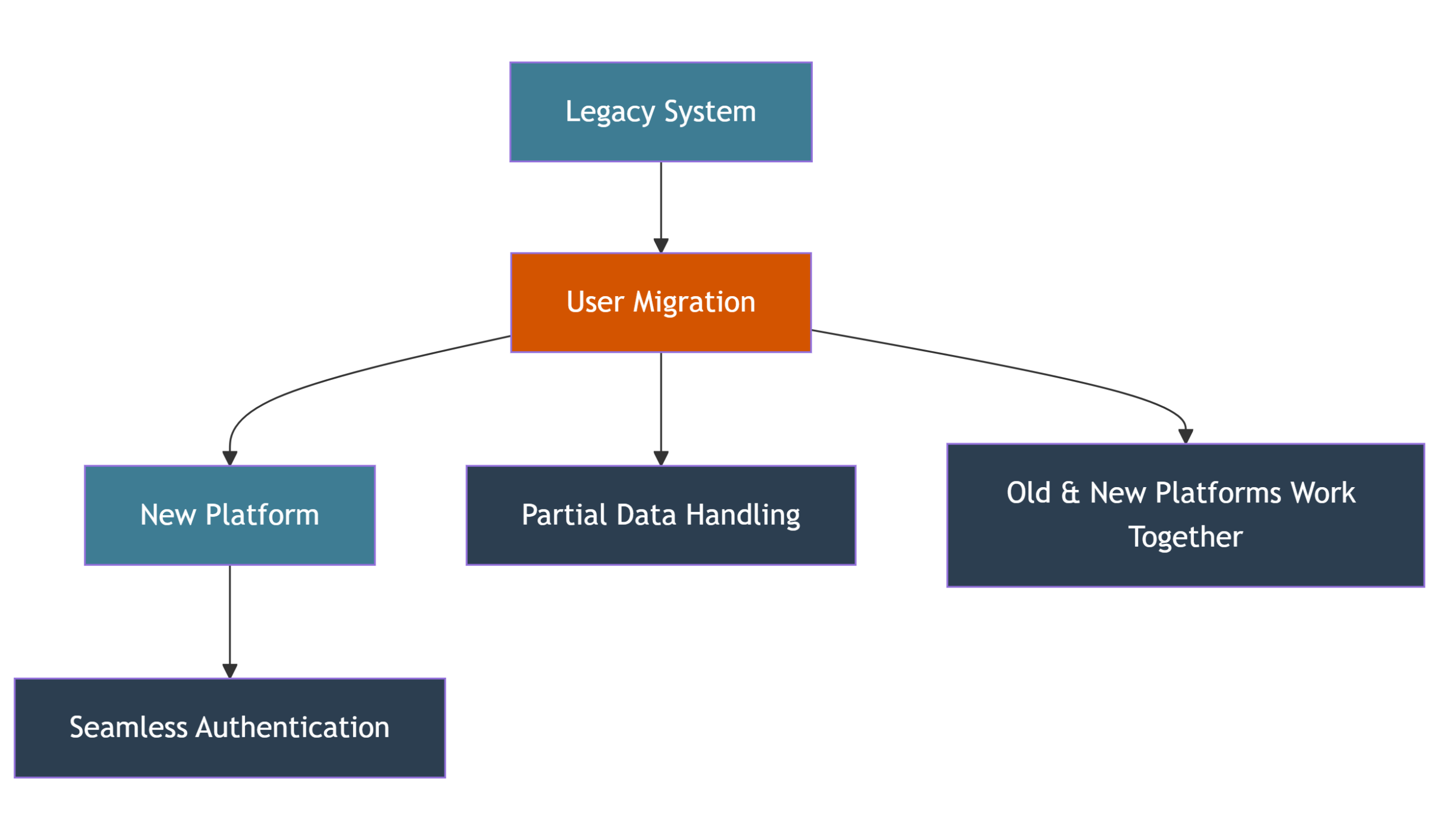
Seamless migration (Inteca’s daily job)
Most onboarding projects aren’t greenfield. Old systems, old accounts, old data – they all stay.
The challenge? Make sure migrating users don’t feel it.
At Inteca, we specialize in migrations where:
- Users move smoothly between systems.
- Old and new platforms work together.
- Authentication just works — even when data is partial.
Users should notice the change only when they get faster access – not when something breaks.
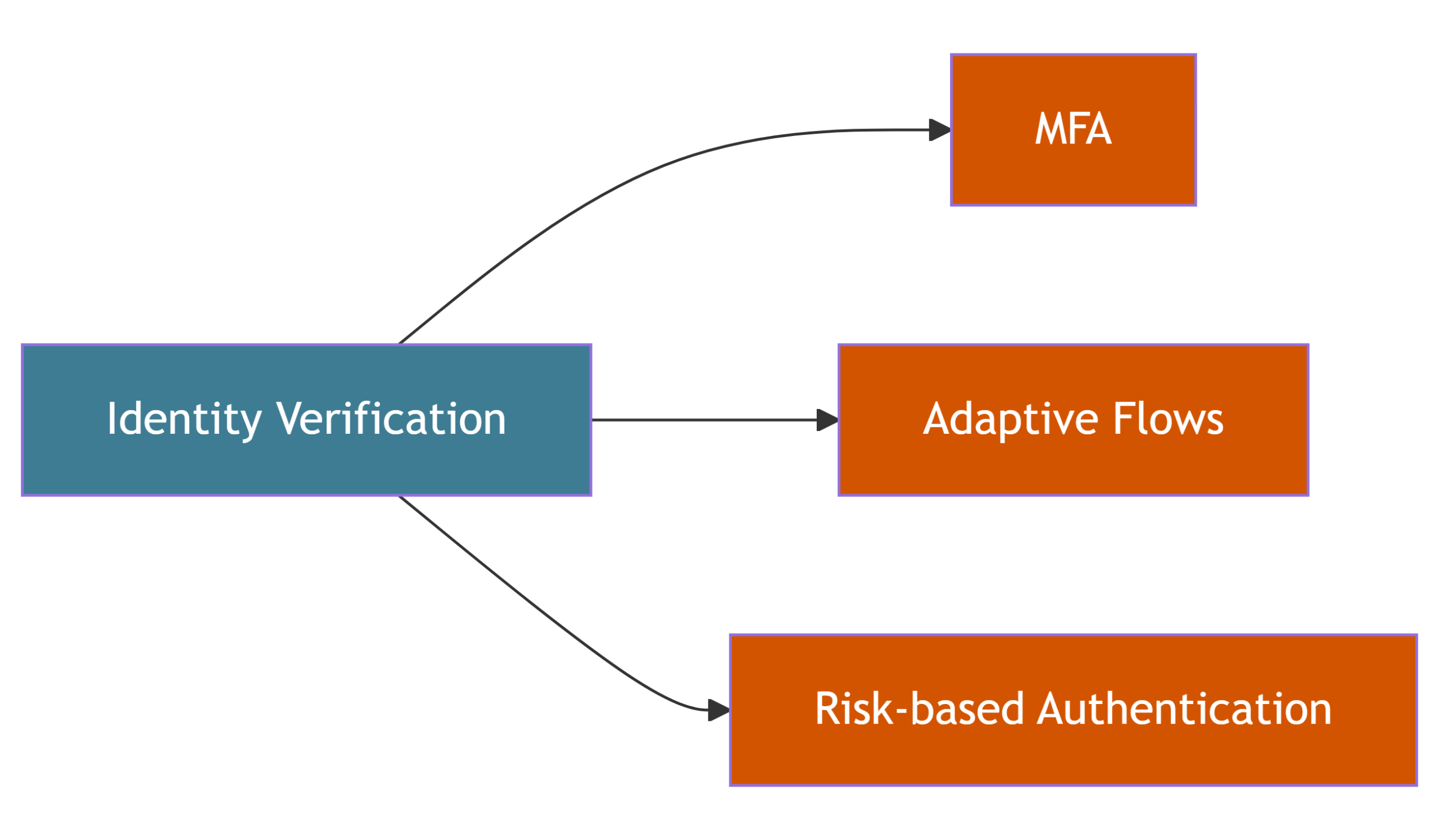
Advanced identity verification — without making users suffer
Identity verification is critical. You can’t cut corners here.
But there’s no need to frustrate users. Modern IAM lets you balance security and comfort:
- Multi-Factor Authentication (MFA)
- Adaptive flows – stronger verification when needed, smoother when risk is low
- Risk-based authentication – more security only when the situation calls for it
Make users feel safe. Not suspiscious.
Dynamic consent management
Consent isn’t just a pop-up. It’s part of the onboarding flow.
Good IAM lets you:
- Collect GDPR, RODO, and marketing consents directly during onboarding.
- Adapt consents depending on user type or flow.
- Make consent management simple and compliant – without ruining UX.
Inteca builds consent into IAM from the start. Users stay informed. Organizations stay safe.
Automated role assignment
Users shouldn’t wait days for someone to click “approve”.
Neither should admins fix roles manually after onboarding.
IAM should:
- Assign roles automatically based on onboarding paths, user types, or attributes.
- Handle even complex role logic without human errors.
- Enforce role-based access control (RBAC) right from the start of the application.
We helps clients automate this step fully. Users get the access they need
Designing modern onboarding flows
Good onboarding is never just about security. It’s about design. About feeling. About getting end users from “I’m here” to “I’m ready” fast and safe through streamlined processes. Don’t forget that users give you their personal data, access to their devices. They need to feel that their information is safe with you.
Most companies start with the same problem. They design login flows on whiteboards, mockups, or Figma screens — but they miss how IAM actually works.
Our clients?
They want:
- onboarding that fits their business logic,
- onboarding that makes sense for their users,
- onboarding that works with their legacy systems,
- onboarding that plays nicely with UX research outcomes.
That’s where things get tricky.
Security, UX, business rules all have to meet halfway.
And Inteca is responsible for security.
UX + IAM design
You can’t separate UX from IAM.
No matter if it’s a customer or employee, onboarding is their first interaction with your system.
IAM isn’t just “backend stuff.” It shapes the experience:
- How fast users register.
- How they verify their identity.
- How they grant consents.
- How roles get assigned.
The best onboarding? It feels effortless. But behind the scenes — it’s pure IAM craftsmanship.
Sample onboarding flow (real-life inspired)
Here’s what a modern, IAM-driven onboarding often looks like:
- User lands on the registration page.
Chosen flow: email, phone, social login, or passwordless. - Identity gets verified.
Simple or advanced — depending on user type and risk level. - Consent step.
GDPR, marketing, RODO — embedded, dynamic, compliant. - Role assignment.
Based on data or user path — fully automatic. - Welcome.
User lands in their dashboard with the exact access they need.
Nothing more, nothing less.
That’s onboarding — clean, safe, fast.
But real life? It’s messier.
Users will:
- abandon flows,
- close the browser halfway,
- get stuck on verification,
- migrate from legacy systems with only half the data.
Good onboarding handles it.
Fallback flows, alternative paths, smart handling of incomplete cases — that’s part of the IAM logic too.vWith Inteca, even broken journeys have a way forward.
Inteca’s Role in IAM Onboarding
Modern onboarding needs more than just a tool. It needs someone who will make sure it works — for users, for business, and for security.
Inteca as advisor, designer, integrator, and operator
At Inteca, we don’t just install IAM systems.
We help clients solve the whole onboarding puzzle.
From day one, we act as:
-
Advisor — showing how onboarding should look from a security and UX perspective.
-
Designer — helping clients shape login flows that actually fit their users and business.
-
Integrator — connecting IAM with legacy systems, APIs, and modern platforms.
-
Operator — maintaining and improving IAM when things go live.
Our clients don’t want another project.
They want an onboarding flow that feels like part of their product — smooth, secure, and flexible.
And that’s exactly what we do.
Old accounts are one of the biggest risks in modern IAM
Keyckoak in IAM onboarding – why
We don’t reinvent the wheel. We use Keycloak the most proven open-source IAM solution, supported by Red Hat. We not only support open-source but also licensed version of Keycloak – Red Hat Built of Keycloak.
Why? Because it’s:
- Secure.
- Flexible.
- Ready for custom onboarding flows.
Keycloak gives us full control. We can adapt it to even the most demanding onboarding scenarios. From simple employee onboarding to multi-platform, multi-role customer onboarding. And we know how to make Keycloak sing.
Over the years, we’ve built a library of real onboarding patterns:
- Flexible sign-up flows – email, password, social login, passwordless, basically any verification method can be applied to Keycloak system.
- Dynamic consents from GDPR, RODO, marketing consents fully integrated into onboarding.
- Role assignment automation based on user data, onboarding flow, or custom logic.
- Fallbacks handling edge cases, migrations, or users who drop out and return.
We don’t just build onboarding. We make sure it can survive real-life users, edge cases, and future changes.
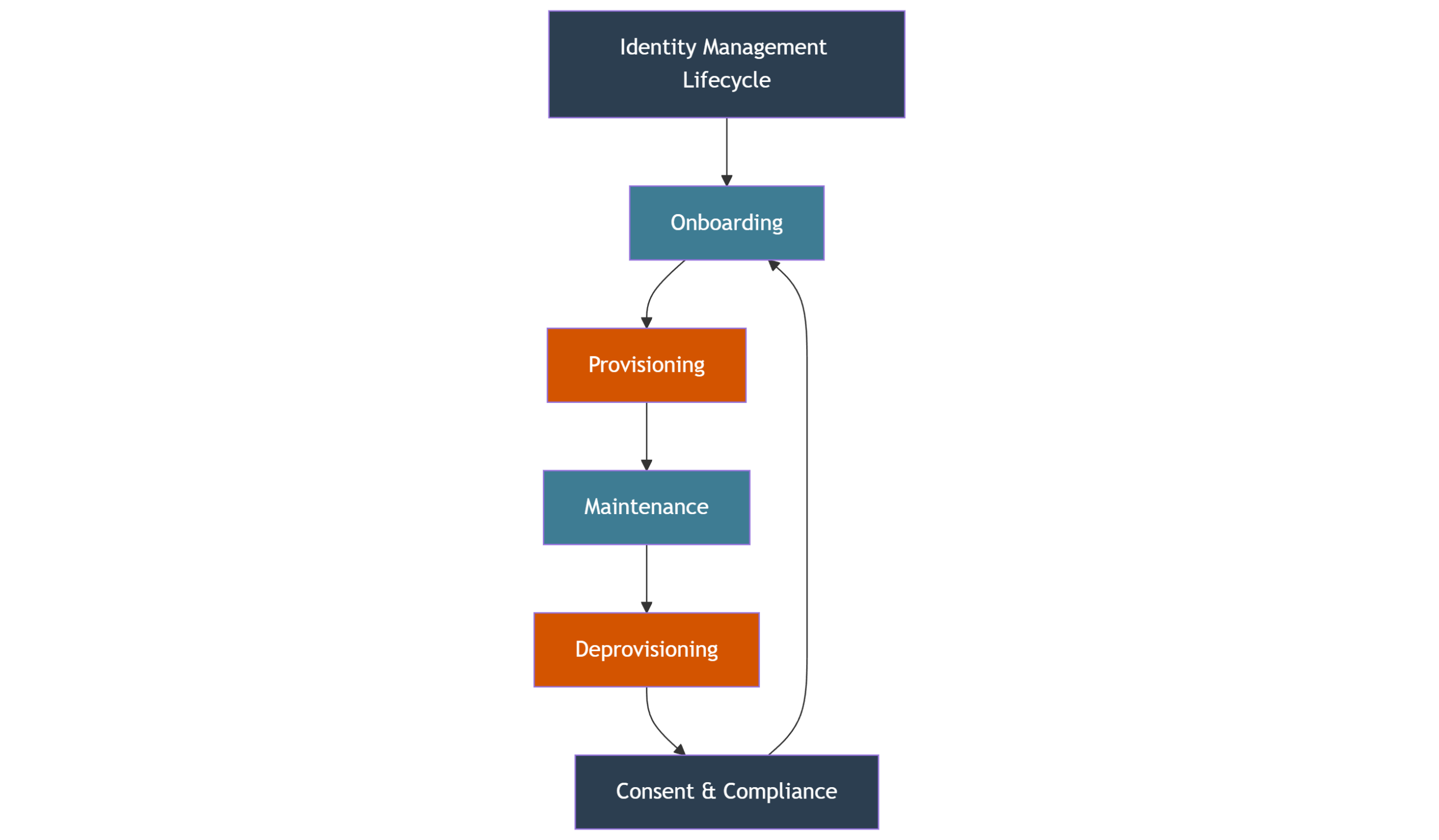
Full Identity Lifecycle, what is beyond user onboarding?
Onboarding is just the beginning. Secure access management isn’t a one-time thing. It’s a cycle. A lifecycle. Every user, employee or customer goes through it. From the first login to the last logout. Here’s how modern IAM handles it. See the steps of identity lifecycle process:
Onboarding -the first step, the first impression
It starts with onboarding. The make-or-break moment.
Create accounts, verify identity, assign roles, collect consents.
All smooth, secure, and designed for humans, not just auditors.
Good onboarding is more than data collection. It’s the foundation of the user’s relationship with your platform.
Provisioning, granting the right access
After onboarding, users need to get the right privileges.
This stage ensures users have the right access to systems and resources in line with their roles. Good provisioning is essential for security and operational efficiency, and user lifecycle management software can streamline this process.
Provisioning assigns access:
- Based on roles,
- Based on attributes,
- Or based on onboarding paths.
Good provisioning makes sure people have exactly what they need. Automated. Auditable. Adaptable.
Maintenance – staying safe and efficient
Things change. Roles change. Regulations change.
IAM systems and admins need to keep up on:
- Regular updates to user attributes,
- Adjusted permissions when users move between teams or departments,
- Continuous verification of consents.
Proper maintenance means avoiding:
- Orphaned accounts,
- Dormant privileges,
- Forgotten users with admin access.
Deprovisioning & retirement — closing the loop
When users leave – employees or customers- access must disappear. Instantly.
Deprovisioning isn’t just about deleting accounts. It’s about:
- Revoking permissions,
- Removing roles,
- Ensuring regulatory compliance (GDPR, HIPAA, you name it).
Then, when needed, accounts get archived or fully retired. No loose ends. No forgotten data. No privacy nightmares waiting to happen.
The identity lifecycle is simple on paper. But making it work, especially in complex environments, isn’t.
That’s where Inteca steps in.
Automated offboarding and access management
Most companies nail onboarding. Few think about the end. But offboarding? That’s where risk hides. Old accounts. Forgotten permissions. Ex-employees who still have admin access.
That’s not just bad practice. That’s a data breach waiting to happen.
Offboarding needs automation. Not post-its.
You can’t rely on someone “remembering” to disable access.
IAM should:
-
Revoke access instantly when contracts end,
-
Remove roles across all systems,
-
Pull back consents — marketing, GDPR, everything.
Automatically. Reliably. Every time.
Deactivate. Don’t delay.
The second someone leaves, access goes dark.
With Inteca’s approach:
- Accounts are deactivated in real time,
- Sessions are ended across all devices,
- Tokens are invalidated,
- Audit trails show who had access, when, and for how long.
No access gaps. No leftovers.
Consent and compliance? Handled.
Consent doesn’t live forever.
If someone leaves, their data access must end too.
Inteca ensures consent revocation is part of the offboarding flow.
That’s how you stay compliant.
And respectful of user data.
IAM isn’t complete without this step.
Most breaches? Come from forgotten accounts. Most fines? From poor data management.
Offboarding isn’t “optional.” It’s the final, critical step in the identity lifecycle.
And it’s where Inteca makes a real difference.
References
-
DBIR 2024 – Verizon Data Breach Investigations Report
Verizon. (2024). Data Breach Investigations Report. https://www.verizon.com/business/resources/reports/dbir/ -
IBM Cost of a Data Breach Report 2024
IBM Security. (2024). Cost of a Data Breach Report https://www.ibm.com/reports/data-breach -
LayerX State of Access Governance Report 2024
LayerX. (2024). State of Access Governance Report. https://www.layerx.com/research/access-governance-2024
Solving IAM onboarding problems isn’t just theory for us