SSO migration is the process of moving authentication and session control from a legacy SSO or Web Access Management stack to a modern identity provider and standards-based protocols.
What is SSO migration?
SSO migration is the controlled transition of applications from an existing single sign-on implementation (often a legacy WAM, custom SAML, or on-prem federation) to a new SSO architecture.
A complete SSO cutover includes protocol alignment (SAML or OIDC), user lifecycle integration (often SCIM), policy modernization (MFA and conditional access), and operational controls (logs, monitoring, incident response). That scope matters because “login” is a security boundary, not just a UX feature.
Why do SSO legacy applications make migration a security priority?
SSO legacy applications make authentication system migration a security priority because legacy stacks frequently centralize risk in hard-to-patch components and brittle policy logic.
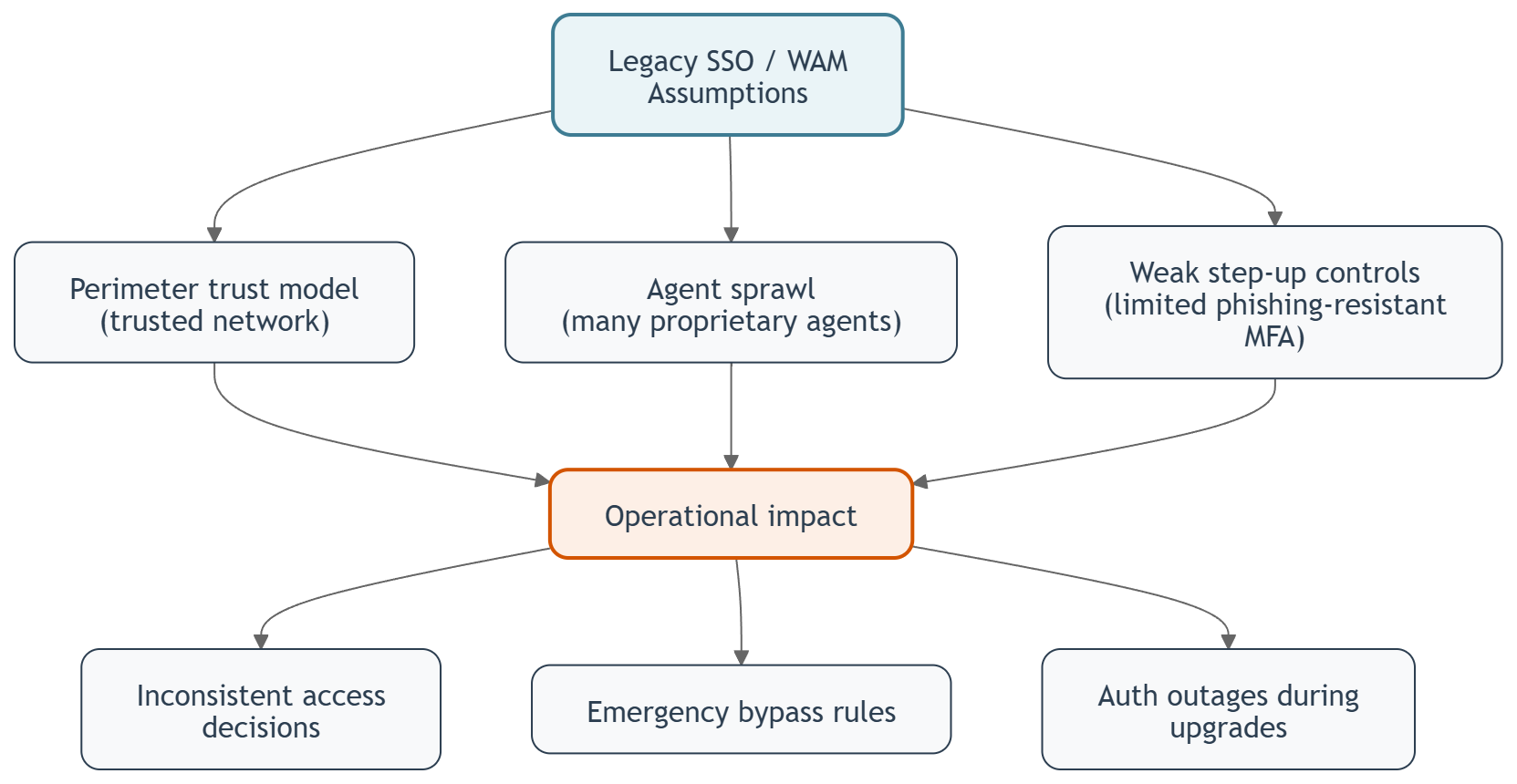
Typical risk patterns include:
- Perimeter assumptions: legacy WAM designs assume trusted networks; modern threat models assume stolen sessions and compromised endpoints.
- Agent sprawl: proprietary web agents across many servers increase patching and regression risk.
- Weak step-up controls: older flows struggle with phishing-resistant MFA and device context.
Those issues surface as real operational incidents: inconsistent access decisions, emergency bypass rules, and authentication outages during routine upgrades.
Which legacy components usually trigger decision about moving from legacy SSO system?
Legacy SSO components that often trigger an SSO migration program include perimeter-based Web Access Management and older federation gateways.
Common examples in regulated enterprises:
- Legacy WAM: CA SiteMinder, Oracle Access Manager, IBM ISAM.
- Legacy federation: AD FS.
These platforms can remain functional, but their architecture often conflicts with Zero Trust principles and modern identity governance requirements. That conflict is the point where “keep it running” becomes “migrate it safely.”
What does a modern SSO stack look like after SSO migration?
A modern SSO stack after SSO cutover is a standards-based Identity Provider layer with centralized policy, strong authentication, and predictable integrations.
A typical target architecture includes:
- Modern Identity Provider (IdP) / IDaaS: Microsoft Entra ID, Okta, or a self-managed enterprise IdP.
- Protocols: SAML 2.0 and OpenID Connect (OIDC) for application sign-in.
- Authorization: OAuth 2.0 scopes and claims-based access.
- MFA: adaptive MFA plus phishing-resistant methods (FIDO2/WebAuthn).
- Provisioning: SCIM user provisioning or HR-driven identity lifecycle.
- Operations: centralized audit logs, SIEM integration, and consistent incident playbooks.
This target model is also the foundation for IAM modernization as a broader program, not only an SSO upgrade.
How do SAML and OIDC decisions affect SSO migration for legacy applications?
SAML and OIDC decisions affect SSO migration for legacy applications because protocol choice determines what you can standardize, what you must translate, and how much refactoring is required.
- SAML is common in older enterprise apps, especially server-rendered apps and vendor products. SAML is stable, but it can be configuration-heavy (ACS URL, Entity ID, certificate rotation).
- OIDC is common in modern apps, APIs, and mobile-first architectures. OIDC typically simplifies token handling and supports modern auth patterns more naturally.
A practical rule: keep SAML where the application already supports it reliably, and adopt OIDC for new development or where you need modern session and token patterns. That leads directly to the next question: how to connect apps that support neither cleanly.
How does an identity proxy enable SSO migration for sso legacy applications without rewriting them?
An identity proxy enables SSO migration for sso legacy applications by acting as a protocol and session translation layer between a legacy app and a modern IdP.
In practice, the identity proxy terminates the modern authentication flow (for example OIDC) and presents a legacy-compatible interface to the application (for example header-based identity, legacy cookies, or SAML assertions). This pattern is especially useful when you cannot modify the application quickly but still need centralized policy and MFA.
What is a low-downtime SSO migration process?
A low-downtime SSO migration process is a phased cutover where identity policy is modernized first and application integrations are moved in controlled waves.
A pragmatic migration process:
- Inventory: list every app, protocol (SAML/OIDC/header), user store, and current sign-in URL.
- Define target controls: MFA requirements, session lifetime, step-up policy, audit logging, break-glass access.
- Build the integration patterns: direct SAML/OIDC, identity proxy, or orchestration.
- Pilot wave: move 1–3 apps with different patterns; validate login, logout, and account linking.
- Parallel run: operate old and new SSO while measuring sign-in success rate and helpdesk tickets.
- Wave migration: migrate by risk and complexity; prioritize internet-facing and privileged apps.
- Decommission: remove old agents, old policies, and unused trust relationships.
The key operational metric is authentication reliability: sign-in success rate, average sign-in time, and incident count during policy changes.
How do you migrate user identities and passwords during SSO migration?
You migrate user identities and passwords during SSO migration by separating identity lifecycle from credential handling, then choosing a safe password transition strategy.
Common approaches:
- Federation-first: keep the authoritative identity in the old directory temporarily, and gradually move provisioning and attributes.
- SCIM provisioning: create accounts in the new IdP and keep attributes consistent.
- Just-in-time (JIT) password provisioning: migrate credentials on first login, reducing forced resets and limiting disruption.
The security requirement is consistency: users must not end up with multiple unlinked identities across apps, because that produces access drift and audit exceptions.
What governance controls should be included in an SSO migration for regulated enterprises?
Governance controls that should be included in an SSO migration for regulated enterprises are auditability, policy traceability, and controlled change management.
Minimum set:
- Audit trail: who changed MFA rules, conditional access, certificates, and app trust settings.
- Access review readiness: clear mapping of apps to roles, groups, and entitlement owners.
-
Certificate rotation process: run scheduled SAML signing/TLS rotations with a dry run in a non-prod environment, a defined test window, and an explicit rollback plan. Validate metadata, certificate rollover behavior, and clock-skew tolerance before production cutover.
-
Break-glass design: privileged accounts with hardware-backed MFA and monitored use.
- Incident playbooks: token theft response, compromised user response, IdP outage response.
This is where Zero Trust becomes concrete: access decisions become contextual and continuously evaluated, not “inside network = trusted.”
What are the most common SSO migration pitfalls in legacy applications?
The most common SSO migration pitfalls in sso legacy applications are protocol edge cases, inconsistent identity attributes, and underestimating logout/session behavior.
Pitfalls that repeatedly cause rework:
- SAML misalignment: wrong ACS URL, Entity ID, NameID format, clock skew tolerance, or certificate rollover gaps.
- Attribute drift: different usernames (UPN vs email vs employee ID) across systems.
- Session confusion: app session lifetime conflicts with IdP session policies.
- Non-standard apps: apps that only support header-based identity or custom login endpoints.
A mitigation pattern is to standardize an “identity contract”: canonical user ID, required attributes, and group/role semantics before large-scale migration waves.
When should you use identity orchestration in an SSO migration?
You should use identity orchestration in an SSO migration when you need to decouple applications from a specific IdP, support multiple IdPs, or gradually transition authentication policies.
Identity orchestration is useful when:
- You run multi-cloud or multiple business units with different IdPs.
- You need policy abstraction (one access policy layer, many downstream apps).
- You expect future migrations (IdP change becomes a configuration change, not an app rewrite).
Orchestration also reduces coupling during SSO migration waves, because apps can integrate once while you change upstream identity components over time.
How does Inteca support SSO migration as part of IAM modernization?
Inteca supports single-sign-on cutover as part of IAM modernization by designing the target identity architecture, implementing integration patterns (SAML/OIDC/proxy), and operating the platform in production.
Inteca’s IAM services are anchored in Identity & Access Management capabilities, including enterprise SSO, federated identity, adaptive MFA, and centralized IAM. For an overview of the modernization services and how SSO migration fits into it, reference to our page https://inteca.com/iam-modernization/.
If your SSO stack includes legacy WAM or AD FS and you need a phased migration plan that supports regulated operations, Inteca’s IAM modernization services provide architecture, implementation, and managed operations.
See Inteca’s approach to IAM modernization projects
FAQ