What is enterprise SSO implementation?
Enterprise SSO implementation is the process of centralizing authentication so users log in once and access many systems securely across internal and external environments.
It supports employees and contractors in internal systems, as well as partners and clients using extranet portals, without repeated sign-ins between connected applications. It reduces password sprawl, improves user productivity, and creates a single policy enforcement point for MFA, conditional access, and audit controls.
In practice, it is one of the fastest ways to improve security posture while simplifying access operations.
What does a practical enterprise SSO framework architecture look like?
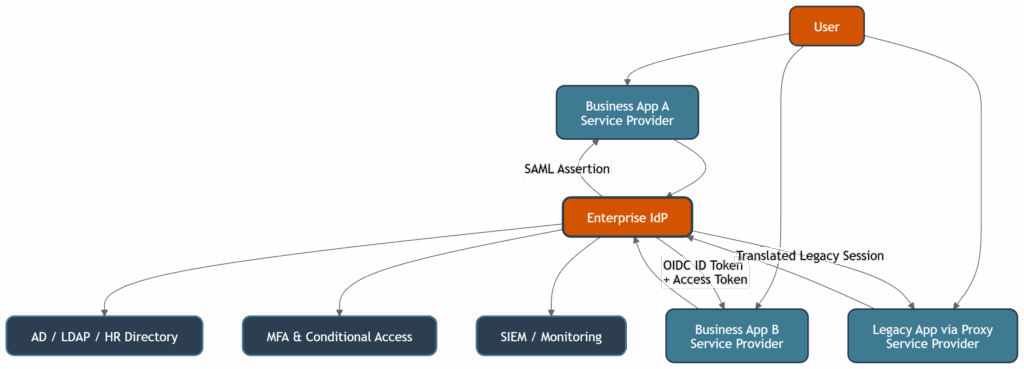
A practical enterprise sso framework has one Identity Provider (IdP), many Service Providers (SPs), centralized policy controls, and integrated directories for different user populations.
The IdP authenticates internal users (employees, contractors) and external users (partners/customers in extranets), evaluates risk controls, and issues protocol-specific artifacts (SAML assertions or OIDC tokens) to SPs.
The same architecture should include high availability, certificate lifecycle management, logging pipelines, and emergency “break-glass” access.
Enterprise SSO framework architecture (sso diagram)
How does IdP vs SP flow work in an enterprise SSO framework?
In IdP/SP architecture, the SP requests authentication and trusts the IdP decision. In SP-initiated flow, a user opens an app, the app redirects to IdP, user authenticates, and the IdP returns a signed assertion or token. The same pattern works for internal business systems and extranet applications, enabling switching between multiple systems within one authenticated session. This model is preferred because the SP can validate request/response state and better mitigate replay and CSRF-like risks.
What should an sso flow diagram include?
An sso flow diagram should show redirect points, authentication checks, token/assertion issuance, signature validation, and session creation on the SP side. It should also include failure branches (MFA required, claim missing, policy blocked) to support operational troubleshooting. This detail is critical for testing and production runbooks.
When should enterprises use SAML, OIDC, or both?
Enterprises usually need both, because application portfolios are mixed. SAML is typically best for legacy or classic enterprise web apps, while OIDC is preferred for modern SPAs, mobile applications, and API-heavy systems. Most production environments run dual protocol support during transition phases.
| Protocol | Best fit | Data format | Typical transport | Main implementation note |
|---|---|---|---|---|
| SAML 2.0 | Legacy enterprise SaaS and B2B portals | XML assertion | Browser front-channel redirects | Strong for federation, heavier operational model |
| OpenID Connect (OIDC) | Modern web/mobile and cloud-native apps | JWT tokens | Hybrid front-channel + backchannel | Better developer ergonomics and API alignment |
| OAuth 2.0 | API authorization, not identity alone | Access tokens | Backchannel API calls | Use with OIDC for authentication |
How should session management be implemented in enterprise SSO?
Session management should use short-lived access tokens, controlled refresh tokens, and centralized revocation. This design limits blast radius after credential theft and enables rapid cut-off when risk increases or accounts are disabled. Mature implementations also support global sign-out and enforce idle/max session boundaries across critical applications.
How should session lifetime be designed in enterprise SSO?
Session lifetime should be risk-based and segmented by user type, application criticality, and access channel (internal vs extranet). A common model uses shorter idle timeouts for privileged/internal admin access and balanced lifetimes for business users who need seamless switching across systems within one session. Good implementation also defines absolute session limits, refresh token rotation, and immediate revocation triggers for high-risk events.
Which enterprise SSO use cases does Inteca deliver in practice?
Inteca delivers four high-value use cases:
- SSO across multiple applications/extranets without re-authentication,
- user session lifetime management,
- SSO for internal users (employees and contractors),
- Switching between systems/extranets within a single session.
These use cases are implemented with policy-driven session controls, protocol federation (SAML/OIDC), and operational monitoring. This approach supports both security and usability goals in real enterprise environments.
What are the key token and assertion controls in enterprise SSO?
Token security requires strict validation rules on every SP. For SAML, validate signature, assertion audience, timestamps (NotBefore, NotOnOrAfter), and replay protection. For OIDC, validate issuer, audience, signature keys, and token lifetime, then enforce minimum claim requirements per application.
How should legacy applications be included in enterprise SSO setup?
Legacy applications should be integrated using secure identity bridges or application proxies when native SAML/OIDC support is missing. This avoids immediate rewrites while still enforcing modern authentication at the edge. A good sso setup maps legacy session expectations (for example Kerberos/header-based models) to modern IdP outcomes in a controlled way.
What are the recommended phases of enterprise SSO implementation?
Successful implementation follows a phased delivery model: discovery, data cleanup, pilot, rollout, and optimization. Discovery inventories applications and protocol readiness; cleanup normalizes identities and claims; pilot validates architecture and UX; rollout introduces staged production traffic; optimization improves policy precision and resilience.
How should testing be handled before production rollout?
Testing should cover protocol correctness, claim mapping, certificate validation, failure handling, and user experience. Include negative tests such as expired certificates, missing group claims, blocked conditional access scenarios, and forced session timeout behavior for both internal and extranet users. Pilot groups should include both technical and business users so rollout decisions are based on real usage patterns.
What should enterprise SSO rollout and monitoring include?
Rollout should be wave-based, with clear communication, rollback criteria, and measurable success metrics per wave. Monitoring should stream authentication, policy, federation, and session telemetry to SIEM for anomaly detection and audit evidence across internal and extranet applications. Teams should track login success rate, MFA challenge outcomes, token errors, session timeout events, cross-application switch success, and certificate expiry windows.
How does Keycloak fit into enterprise SSO configuration?
Keycloak is a strong option for organizations that need open standards, infrastructure control, and flexible deployment models. It can act as central IdP for SAML and OIDC, integrate with enterprise directories, and support advanced policy patterns when properly engineered. In many organizations, Keycloak is used as part of a broader enterprise identity architecture rather than as an isolated tool.
Who can implement enterprise SSO end-to-end?
Inteca implements enterprise SSO for organizations that need secure, scalable, and auditable identity architecture. Our teams deliver full lifecycle services: sso implementation planning, sso architecture design, sso configuration, protocol integration, migration of legacy apps, testing, rollout, and operational monitoring. We also implement Keycloak-based solutions where open architecture and platform ownership are strategic requirements.
Sources
Enterprise SSO services from Inteca
If your organization is planning enterprise sso implementation, Inteca provides architecture-first delivery from assessment to production operations. We design and implement secure SSO platforms, including Keycloak integration, SAML/OIDC federation, session controls, legacy bridge patterns, and SIEM-ready monitoring. Engagement models include advisory, implementation, and managed support for regulated and large-scale environments.
FAQ





